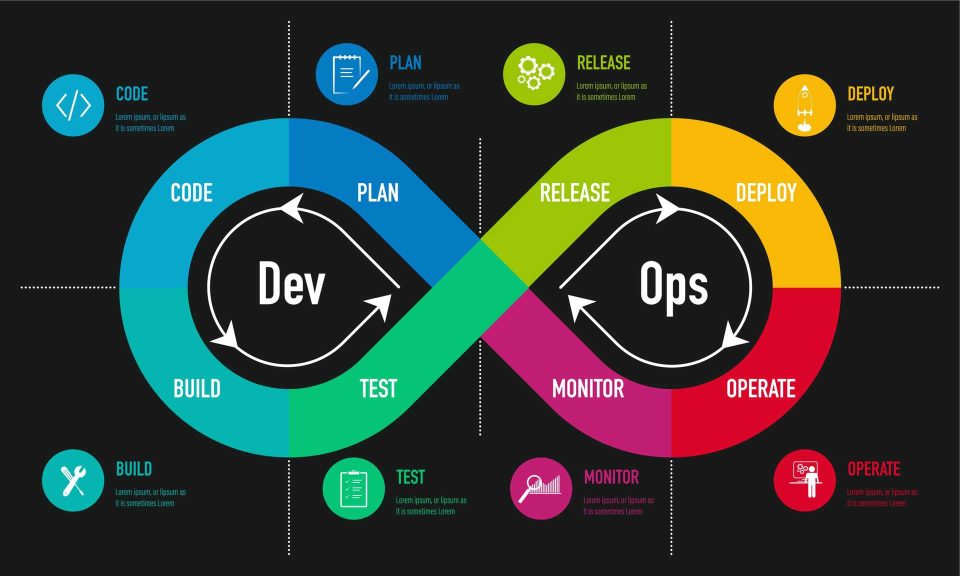
Security breaches rarely occur because teams ignore security altogether. More often, they happen because security checks are introduced too late, when code is already deployed, and changes are expensive. Shift-left security, commonly referred to as DevSecOps, addresses this problem by moving security testing and compliance checks to the earliest possible stages of the development lifecycle. Instead of treating security as a final gate, it becomes a continuous, integrated practice that evolves alongside development and operations. This approach helps organisations reduce risk, accelerate delivery, and build systems that are secure by design rather than by reaction.
Understanding the Shift-Left Security Approach
The idea behind shift-left security is simple. The earlier a vulnerability is identified, the easier and cheaper it is to fix. Traditional models placed security testing near the end of development, often just before release. By that stage, fixing issues could mean rewriting code, delaying launches, or accepting known risks.
In a shift-left model, security considerations start during planning and design. Developers receive early feedback on insecure coding practices, misconfigurations, or dependency risks while they are still writing code. This early visibility prevents vulnerabilities from propagating through the pipeline. Teams adopting this approach often discover that security becomes a shared responsibility rather than a specialised function isolated from development.
Integrating Security into Development Workflows
Effective DevSecOps requires security tools and practices to blend seamlessly into existing workflows. Static application security testing can run automatically as developers commit code. Dependency scanning checks open-source libraries for known vulnerabilities before they are included in builds. Infrastructure-as-code templates can be scanned for insecure configurations before deployment.
These automated checks provide immediate feedback without interrupting productivity. Developers learn from the results and gradually improve their security awareness. Over time, secure coding becomes part of daily habits rather than an external requirement. Professionals exploring modern DevOps practices through devops training in chennai often encounter these integrations as examples of how security and speed can coexist.
Compliance and Policy Checks from Day One
Security is not only about preventing attacks. It also involves meeting regulatory and organisational compliance requirements. Shift-left security ensures that compliance checks are applied consistently from the beginning of the lifecycle.
Policies related to data protection, access control, and encryption can be encoded into automated checks. For example, builds can fail if sensitive data is stored without encryption or if access permissions are overly broad. By enforcing these rules early, teams avoid costly remediation later.
This proactive approach simplifies audits and reduces last-minute compliance surprises. It also creates a clear, repeatable standard for how security and compliance are handled across projects and teams.
Cultural Change and Shared Accountability
Adopting shift-left security is as much a cultural change as it is a technical one. Development, security, and operations teams must collaborate closely rather than working in silos. Security teams shift from being gatekeepers to enablers, providing guidance, tooling, and education.
Developers take greater ownership of security outcomes, understanding how their code impacts overall risk. Operations teams ensure that runtime environments remain secure and observable. This shared accountability builds trust and improves communication across teams.
Learning environments such as devops training in chennai often emphasise this cultural shift, highlighting that DevSecOps success depends on mindset as much as tooling.
Benefits of Shifting Security Left
The benefits of shift-left security are both technical and organisational. Early detection of vulnerabilities reduces rework and accelerates delivery timelines. Automated checks improve consistency and reduce human error. Teams gain confidence in their releases, knowing that security has been continuously validated.
From a business perspective, this approach lowers the likelihood of security incidents that can damage reputation and incur financial penalties. It also supports scalability, as automated security practices can be applied across multiple teams and projects without significant overhead.
Challenges and Practical Considerations
Despite its advantages, shift-left security presents challenges. Too many tools or overly strict rules can overwhelm developers and slow progress. Poorly tuned checks may generate false positives, leading to alert fatigue.
To address these issues, teams should start small and evolve gradually. Selecting the most critical checks, refining rules based on real risk, and helping clear remediation guidance maintain balance. Regular feedback loops between developers and security teams ensure that practices remain practical and effective.
Conclusion
Shift-left security transforms how organisations approach application protection and compliance. By embedding security testing and policy checks early in the development lifecycle, teams reduce risk, improve quality, and deliver faster with greater confidence. DevSecOps is not about adding friction but about creating a secure foundation that supports continuous delivery. As development cycles continue to accelerate, shifting security left is no longer optional. It is an essential practice for building resilient, trustworthy software systems.